Most teams building AI agents pick a SaaS integration pattern by default because hardcoding API calls is the fastest path to a working demo. That shortcut often becomes the first production bottleneck.
AI agents do not just need access to SaaS systems; they need fresh, normalized, permissioned context that can be queried reliably across many sources. The wrong pattern shows up first as auth sprawl, stale context, schema inconsistency, or missing governance.
The right choice comes from comparing patterns by the production constraint you cannot afford to break first.
TL;DR
- SaaS integration architecture patterns determine how AI agents access enterprise SaaS data, with tradeoffs in authentication complexity, data freshness, schema normalization, and governance enforcement.
- Point-to-point API integration and unified API integration fit early prototypes and quick multi-source reads.
- Agent connector platforms with replication fit production AI agents that need managed auth, normalized data, and governed access at scale.
- Hybrid architectures combine direct API access for time-sensitive data with a replicated store for broad historical context.
What Are SaaS Integration Architecture Patterns?
SaaS integration architecture patterns are the structural blueprints that determine how data moves from SaaS applications such as customer systems, chat tools, file stores, and knowledge bases into systems that consume it, including AI agents.
The EIP catalog defines 65 messaging patterns, including message channels, pipes and filters, content-based routers, and message translators. Those concepts still appear in modern systems built on Kafka, Amazon Simple Queue Service (SQS), and Amazon EventBridge.
Modern SaaS integration for AI agents adds variables the classical patterns never anticipated: heterogeneous Open Authorization (OAuth) implementations across providers, unstructured file types alongside structured records, and the requirement for agents to inherit user-level permissions on every query.
Traditional frameworks assess volume, latency, directionality, and protocol, but they were designed for a different consumer.
Why Classical Patterns Fall Short for AI Agents
Classical patterns assume human-driven consumers interacting through UI dashboards, people who can spot a stale number or recognize they are looking at the wrong account.
AI agents are autonomous consumers that need normalized, permissioned, fresh context delivered directly to Large Language Model (LLM) context windows. An agent receiving the amount ‘9900’ from a payment system, in cents, and reasoning about it as $9,900 in a dollar-denominated customer system context does not self-correct.
What Do the Seven SaaS Integration Patterns Look Like?
Point-to-Point API Integration
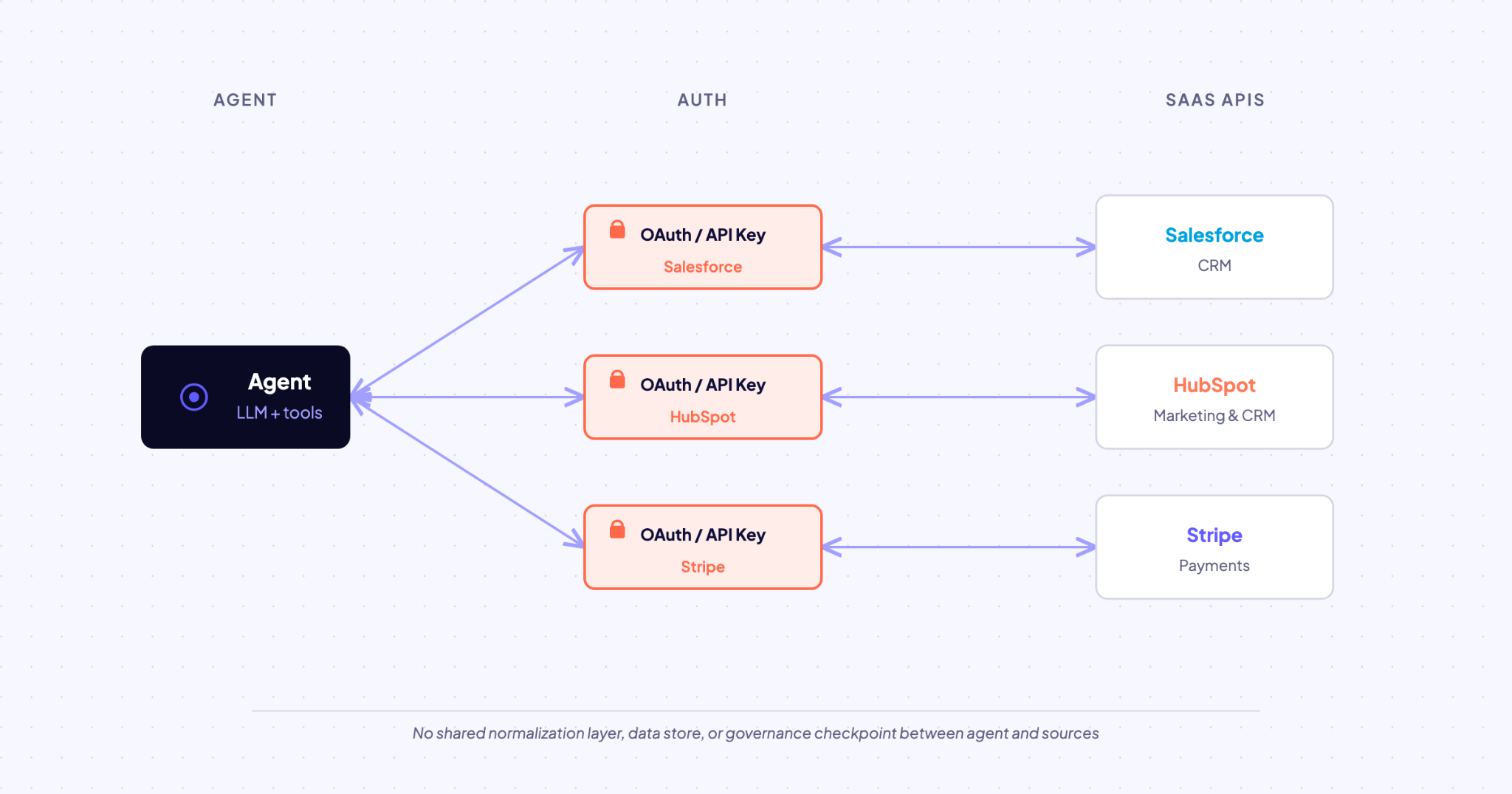
The agent calls each SaaS API directly, managing credentials, request construction, response parsing, and error handling independently per provider. Each new source requires a new dedicated connection with its own auth logic.
Best for: Prototypes with 1–3 sources where you need a working demo this week.
Watch for: Auth sprawl hits fast. Management is still manageable at 5 integrations, but at 20+ it becomes a system reliability problem. Without a normalization layer, the agent receives raw, provider-specific schemas, contact_name from one API and full_name from another, with nothing to reconcile them.
Webhook-Driven Event Integration
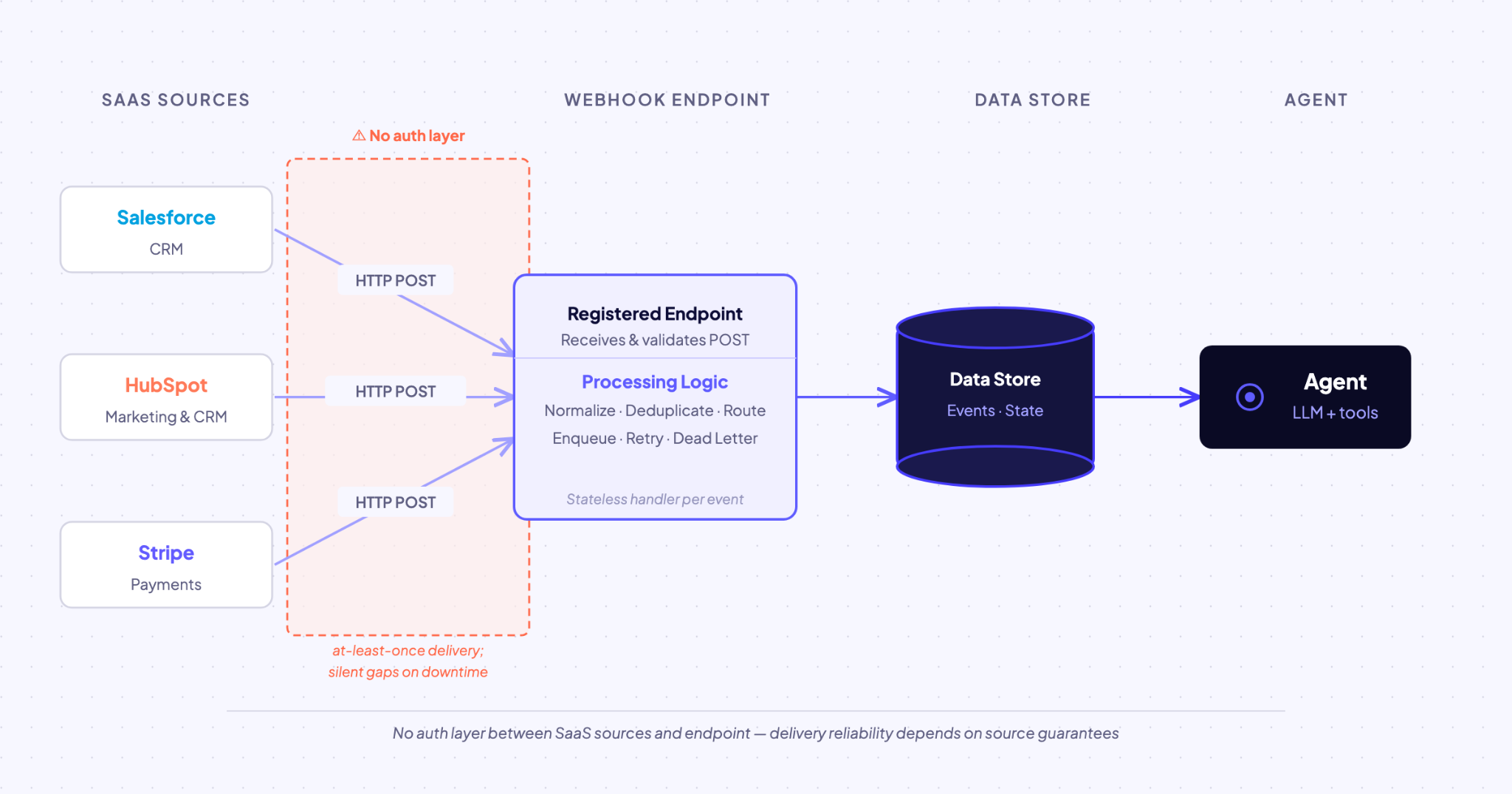
The source SaaS initiates the push. Your endpoint must be publicly reachable and respond within the provider's timeout window. Teams often need a compensating GET call to fetch full record state, which adds latency and a second failure point.
Best for: Trigger-based workflows with SaaS apps that emit events reliably.
Watch for: Missed webhooks can remove data from agent state if no mechanism exists to retransmit data when your endpoint is down. Event delivery may also arrive out of order, governance is not built in, and the pattern is limited to events the source is configured to emit.
Unified API Integration
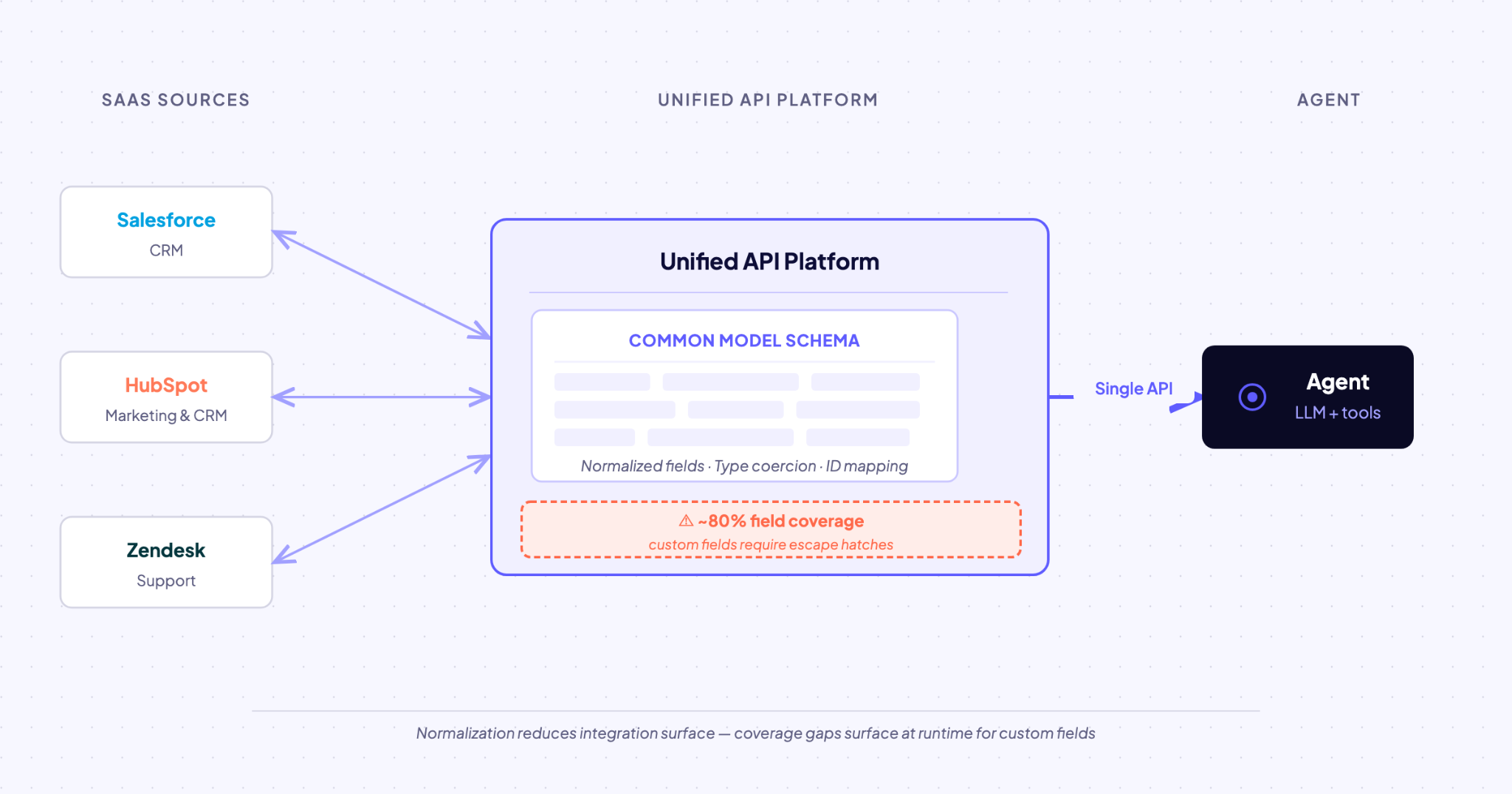
The platform polls source APIs on a schedule, normalizes responses into a common schema, and exposes a single API to your agent. You get one auth flow, one query language, and one response format.
Best for: Quick multi-source reads when partial field coverage is acceptable.
Watch for: The common model can include only features all APIs support, so provider-specific capabilities are lost. Unified APIs also create a single normalized interface that abstracts over provider-specific query languages, which gives the agent another interface to navigate.
iPaaS and Automation Platform Integration
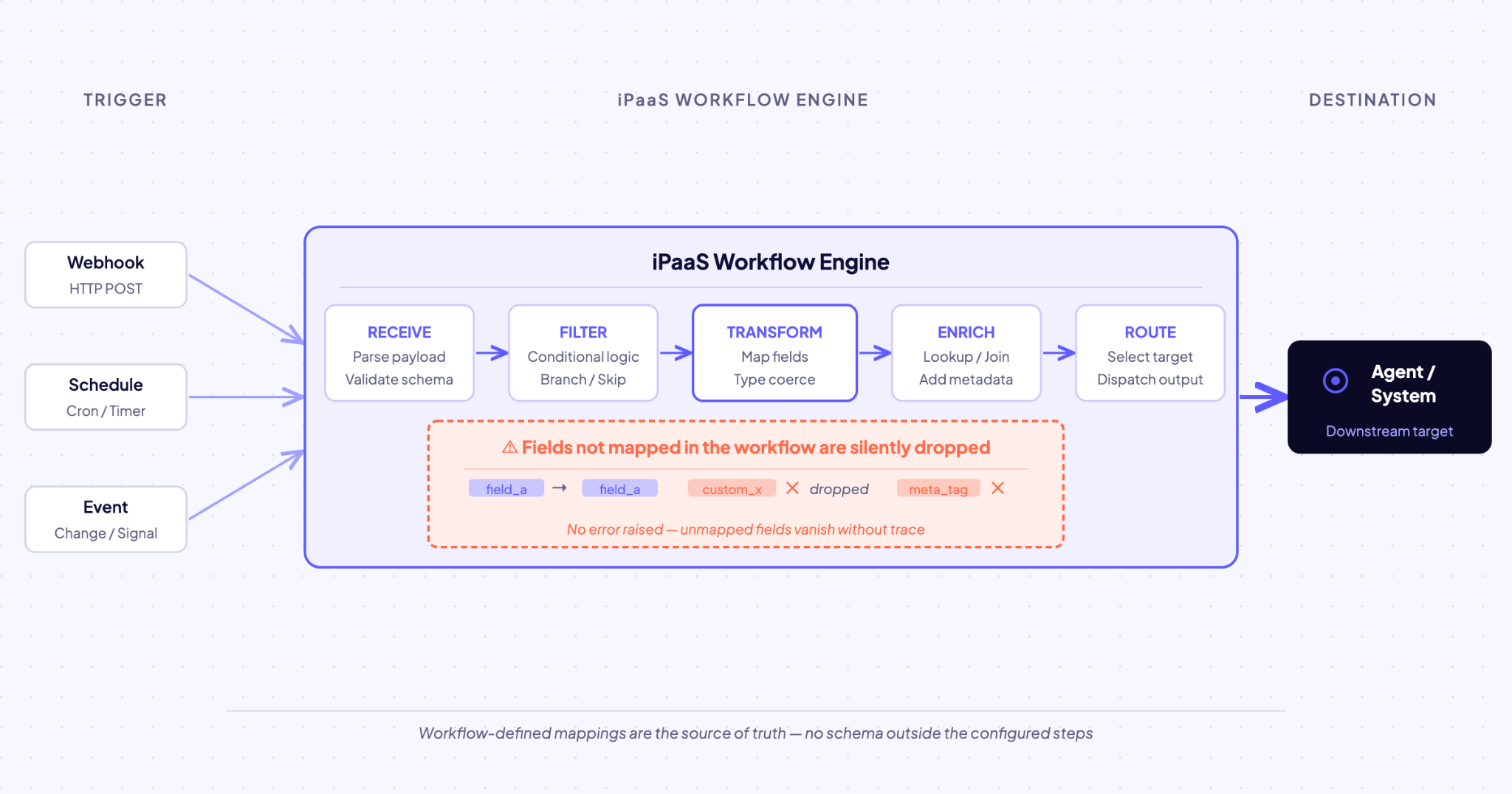
A visual workflow builder orchestrates connections between SaaS apps. An iPaaS manages trigger detection, step sequencing, and action execution.
Best for: Non-technical teams connecting SaaS workflows with pre-built recipes.
Watch for: iPaaS platforms were designed for human-configured, fixed workflows, not dynamic, LLM-driven tool calls. Audit gaps become a problem because execution logs record workflow steps but not agent reasoning, the inputs that triggered the workflow, or what the agent did with the output.
Custom Middleware and Backend for Frontend Integration
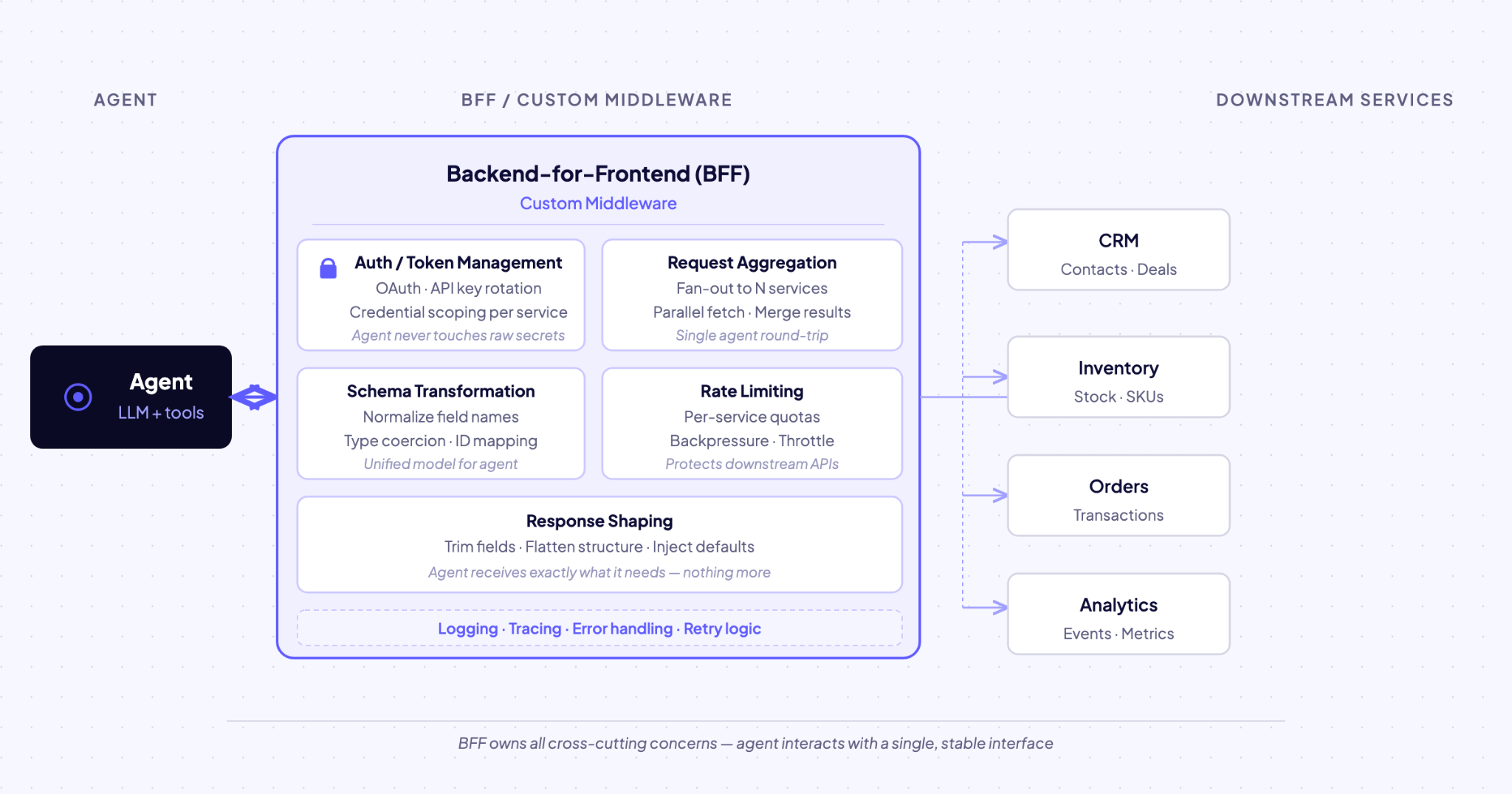
A Backend for Frontend (BFF) is a pattern created for each specific consumer type, where a single call from the agent results in multiple downstream calls to microservices. The BFF aggregates, transforms, and shapes data specifically for the agent.
Best for: Teams with dedicated integration engineers who need full control over normalization and caching.
Watch for: The main cost is building and maintaining every layer yourself. Each new SaaS source requires custom auth logic, schema mapping, and error handling, and those costs compound as the number of sources grows.
Agent Connector Platform With Replication
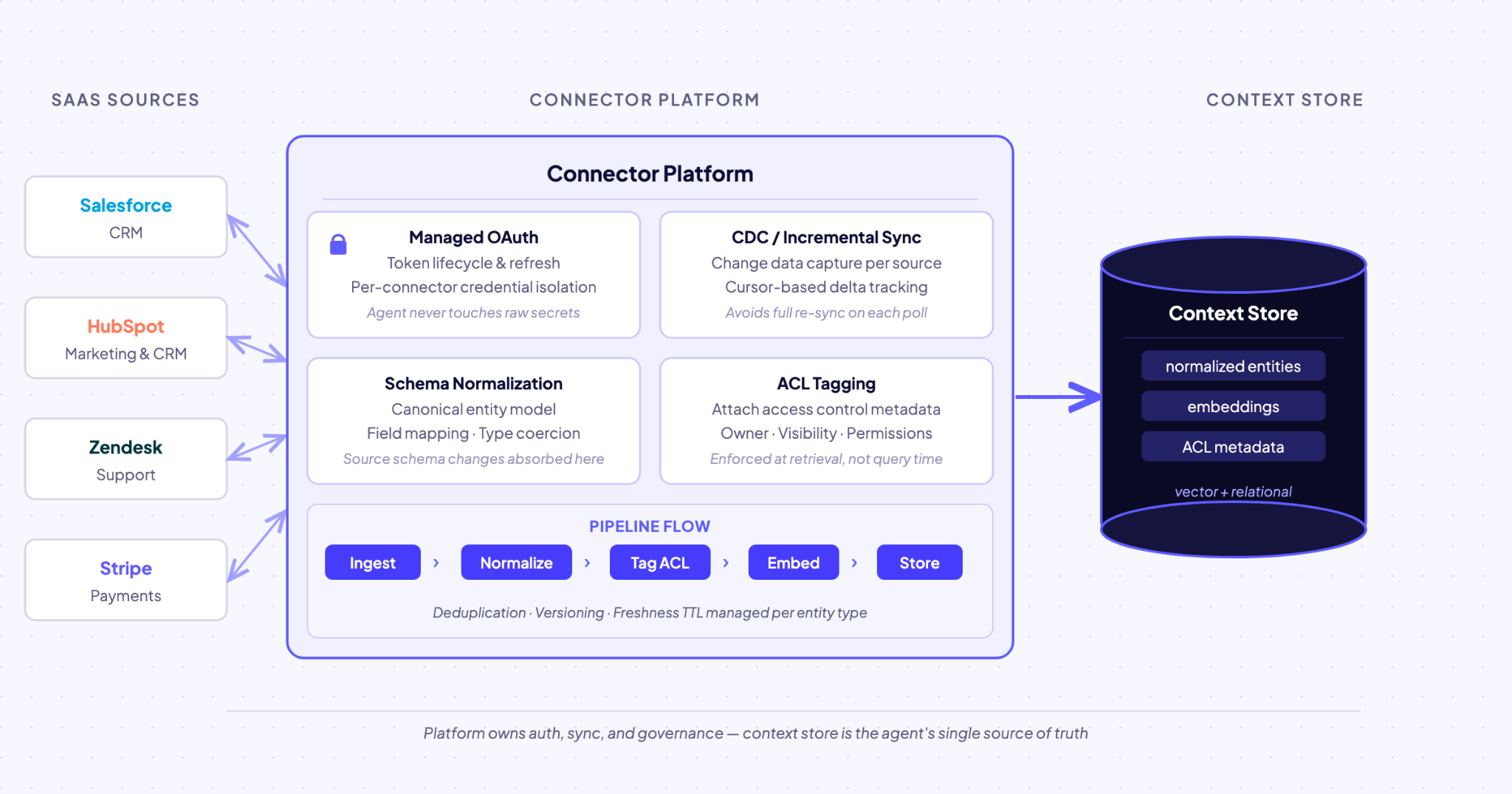
Agent connector platforms can replicate SaaS data into a context store where entities are resolved across sources. The platform manages authentication and token refresh, handles schema evolution, and applies governed access controls at sync and query time. The agent queries the store with sub-minute access instead of hitting upstream APIs for every request.
Best for: Production AI agents that need managed auth, governed access, and normalized data across many sources.
Watch for: Requires configuration up front. Replication introduces sync lag. CDC reduces this to sub-minute, but binary log-based CDC cannot apply directly to SaaS APIs because the underlying database is inaccessible.
Hybrid Live Query Plus Replicated Store
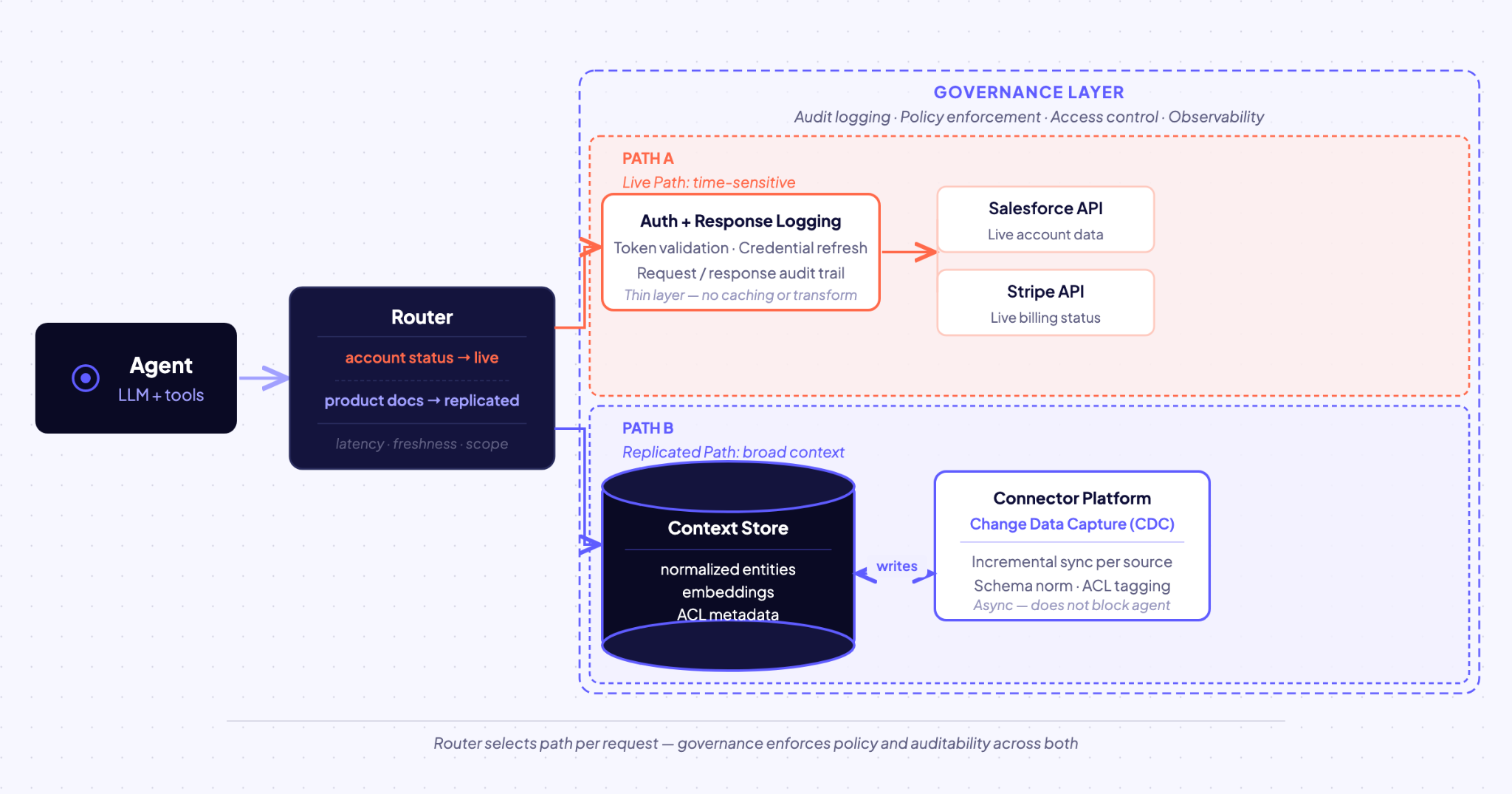
This pattern combines direct API access for time-sensitive data with a replicated store for broad historical context. The architecture derives from Command Query Responsibility Segregation (CQRS), separate structures for reading and writing, with an explicit communication mechanism between them.
Best for: Agents that need both current and historical SaaS data; for example, a support agent checking live account status while searching replicated documentation.
Watch for: The main risk is keeping governance enforcement consistent across both paths. The CQRS model might not reflect the most recent changes immediately, and for agents issuing sequential queries within a short reasoning window, that staleness exposure compounds.
How Do You Compare SaaS Integration Patterns for AI Agents?
Compare patterns by asking four operational questions: who handles authentication, how fresh the data is, whether schemas are normalized, and how governance is enforced.
Point-to-point API integration sits at one end of the range, with high auth complexity, request-time freshness, and no built-in normalization or governance.
An agent connector platform with replication sits at the other end, with managed authentication, incremental-sync or CDC-style freshness, and governed access enforcement.
The table below condenses the tradeoffs across the seven patterns.
Which Pattern Fits Your Agent's Requirements?
Start with your agent's primary requirement, then identify which patterns satisfy it and which create friction.
Scenario 1: Startup prototype. You are building a demo with Salesforce, Slack, and Notion data. You need it working in under two weeks. Point-to-point API calls or a unified API are the right choice. The overhead of setting up a connector platform is not justified yet. Plan to revisit when you start onboarding customers with their own data.
Scenario 2: Enterprise support agent. Your agent queries Salesforce, Zendesk, and Confluence on behalf of individual support reps. Each rep should only see their own accounts. A pattern can provide built-in ACL propagation, so the agent's queries inherit the requesting user's permission scope. Without this, you would need to build auth enforcement at the point of document retrieval, before data enters the agent's context, from scratch.
Production systems often combine multiple patterns as requirements change.
Where Do Most Teams Get Stuck When Patterns Evolve?
Teams usually get stuck when the pattern that worked first stops working cleanly as the number of sources, users, and controls grows. Those friction points are not failures but engineering tradeoffs that become more visible at scale.
Authentication Sprawl
OAuth token refresh, scope differences, and credential rotation across 15+ SaaS providers become their own infrastructure problem because each provider implements OAuth differently. Teams then need distributed locking, grace periods, and explicit re-auth fallback.
Schema Drift and Normalization Debt
Each SaaS API defines common business objects differently. One system may split account, contact, and lead into separate objects, while another may use a single contact object with lifecycle properties. A payment system may define a customer as anyone with a record, including people who have not purchased, and amounts may be specified in the smallest currency unit, for example, cents.
Without a normalization layer, agents receive inconsistent data, and that inconsistency raises reasoning and retrieval errors even when calls are structurally valid.
Retroactive Governance
Adding row-level access controls after an integration reaches production requires re-architecting data flows. A service account model that never captured user identity at query time cannot add filtering retroactively because no identity exists to filter on. Most teams discover this requirement during their first enterprise security review, when the integration is already load-bearing.
These friction points often push teams from patterns 1–4 toward patterns 5–7.
What Is the Fastest Way to Get Your Agent Into Production?
Decide which constraint matters first: authentication overhead, freshness, normalization, or governance. Score each pattern in the comparison table against that constraint, rule out patterns that fail it, and deprioritize patterns that force you to build what you need from scratch.
Most teams can narrow the field to one or two candidates within a single working session. For teams evaluating the agent connector and tool layer together, Model Context Protocol (MCP) still sits above the SaaS integration pattern layer rather than replacing it, so the pattern choice you make here applies regardless of whether you adopt MCP later.
Airbyte Agents aligns with the agent connector platform with a replication pattern and supports hybrid architectures. It provides managed auth and token refresh, unified handling of structured records and files such as contracts and PDFs, automatic embedding generation and metadata extraction, governed access controls, audit logging, and deployment options that include cloud, multi-cloud, on-prem, and hybrid.
The Context Store continuously replicates and caches SaaS data into a local store where entities are resolved across sources, and direct agent connector access supports live fetches for time-sensitive lookups.
Get a demo to see how we support production AI agents with reliable, permission-aware data.
Frequently Asked Questions
What is the difference between SaaS integration patterns and enterprise integration patterns?
Enterprise integration patterns describe abstract messaging and data movement approaches that apply across many systems. SaaS integration patterns focus on connecting cloud applications with heterogeneous APIs, OAuth implementations, and schema conventions. For AI agents, they also need to account for data freshness, normalization, and user-level permission propagation.
Can teams use multiple SaaS integration patterns together?
Yes. Many production agent systems combine patterns rather than choosing only one. The main constraint is keeping governance enforcement consistent across both paths so agents do not see different permissions depending on where data came from.
How does Model Context Protocol relate to SaaS integration patterns?
Model Context Protocol (MCP) standardizes how AI agents discover and call tools. It operates at the agent-to-tool communication layer above the SaaS integration pattern layer. An MCP server still needs reliable agent connectors, normalized data, and access controls underneath it.
When should teams move beyond point-to-point API integration?
The transition point usually arrives when maintaining per-source authentication, handling schema changes, and debugging stale data consume more engineering time than building agent features. That is often the signal that the integration pattern, not the agent logic, has become the main source of drag.
How do SaaS integration patterns influence AI agent accuracy?
Patterns shape whether agents see stale, inconsistent, or permission-misaligned data. Fresher syncs and entity normalization produce higher-quality context, which reduces hallucinations and reasoning errors. Better context does not guarantee good outputs, but weak context reliably creates bad ones.
Try Airbyte Agents
We're building the future of agent data infrastructure. Be amongst the first to explore our new platform and get access to our latest features.
.avif)

